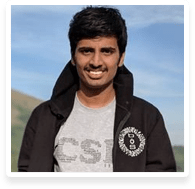
Anirudh Anand
Job Role/Handle- Security Trainer at 7ASecurity, Security Engineer at CRED
Company/Organization- Security Trainer at 7ASecurity, Security Engineer at CRED
Country- India
Place of residence- Bangalore, India
Anirudh Anand is a security researcher with a primary focus on Web and Mobile Application Security. He is currently working as a Senior Security Engineer at CRED and also Security Trainer at 7asecurity. He has been submitting bugs and contributing to security tools for over 7 years. In his free time, he participates in CTF competitions along with Team bi0s (#1 security team in India according to CTFtime). His bounties involve vulnerabilities in Google, Microsoft, LinkedIn, Zendesk, Sendgrid, Gitlab, Gratipay and Flipboard.
Anirudh is an open source enthusiast and has contributed to several OWASP projects with notable contributions being in OWTF and Hackademic Challenges Project. He has presented/trained in a multitude of conferences including c0c0n 2019, BlackHat Arsenal 2019, BlackHat Europe Arsenal 2018, HITB Dubai 2018, Offzone Moscow 2018, Ground Zero Summit Delhi 2015 and Xorconf 2015.