UPDATE: This probably only affects the VMWare image, you will know if it also affects the Kali install if your hashes match my sample hashes below.
So the fine folks at offensive security released this new distro called "Kali Linux" recently, which is essentially:
- Replacing Backtrack
- Based on Debian (instead of Ubuntu)
One of the things that has changed from Backtrack is that it is no longer necessary to generate ssh keys, this is a bit scary for us paranoid security folks as can be seen in this great blog post. In short, having known ssh key pairs available for the whole planet means anybody could MiTM your ssh connections to Kali by default, not cool.
The question is: How do we fix this?
In Backtrack we used to call "sshd-generate" to generate OR overwrite the host ssh keys. However, in Kali if you call sshd-generate you get this:
# sshd-generate
bash: sshd-generate: command not found
The way to "sshd-generate" in Kali is as follows:
Step 1) Move the default Kali ssh keys somewhere else
This way you can use the keys for pranks to your buddies via SSH MiTM and TCP hijacking :).
# cd /etc/ssh/
# mkdir default_kali_keys
# mv ssh_host_* default_kali_keys/
Step 2) Regenerate the keys
# dpkg-reconfigure openssh-server
Creating SSH2 RSA key; this may take some time ...
Creating SSH2 DSA key; this may take some time ...
Creating SSH2 ECDSA key; this may take some time ...
insserv: warning: current start runlevel(s) (empty) of script `ssh' overrides LSB defaults (2 3 4 5).
insserv: warning: current stop runlevel(s) (2 3 4 5) of script `ssh' overrides LSB defaults (empty).
Step 3) Verify ssh key hashes are different now:
# md5sum ssh_host_*
(these are your new keys, compare these hashes to the hashes below)
# cd default_kali_keys/
# md5sum *
b9419ea3a8fff086c258740e89ca86b8 ssh_host_dsa_key
f9a5b57d7004e3740d07c5b037d15730 ssh_host_dsa_key.pub
58e49e0d7b24249c38db0c9cf595751b ssh_host_ecdsa_key
597c83fabf3c1e4f2c7af74af05ac671 ssh_host_ecdsa_key.pub
cc0d92036bb86797bed354338faa7223 ssh_host_rsa_key
cc9ddc90b891b5251ed4ea8341495e84 ssh_host_rsa_key.pub
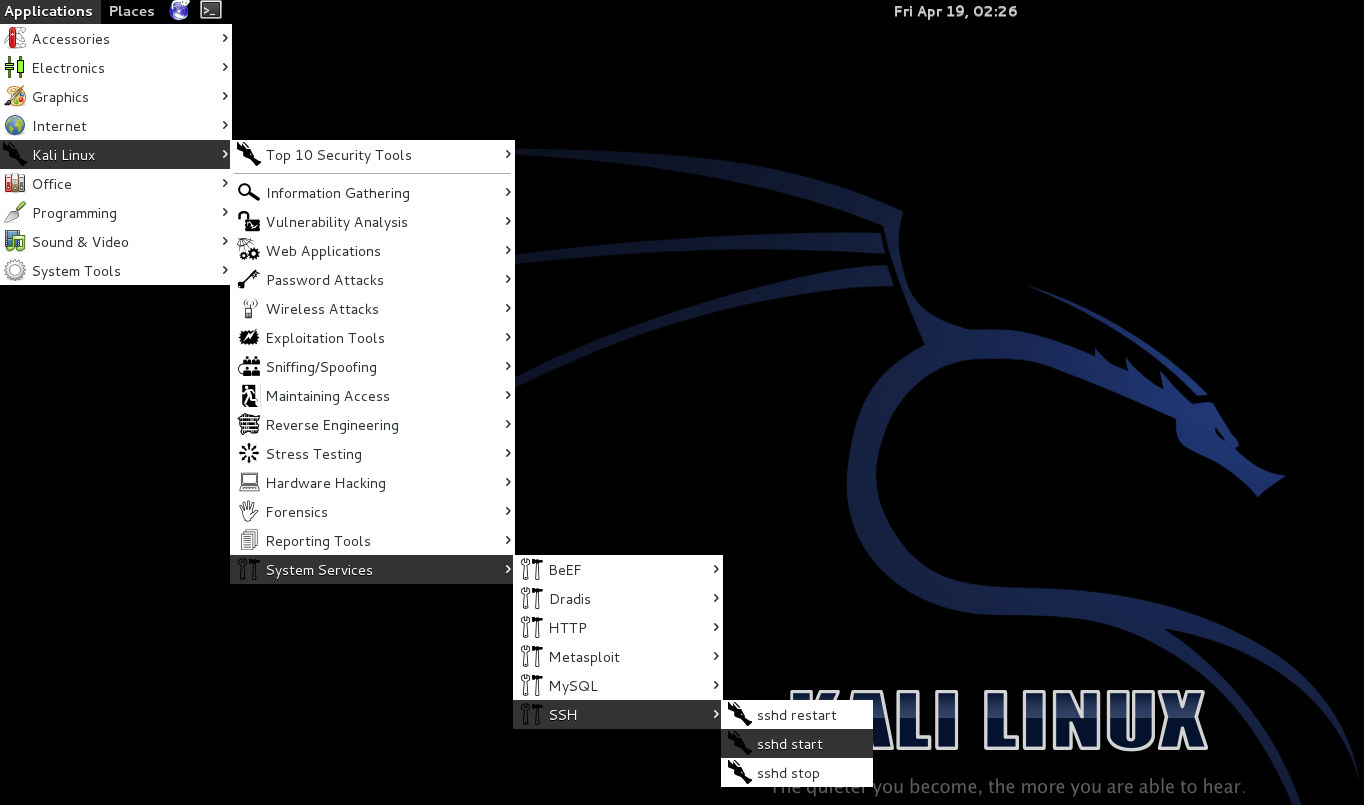
After regenerating the SSH key pairs you can start the SSH service via /usr/sbin/sshd from the CLI or just indulge in laziness and use the menus 🙂
NOTE: Despite the similar name, ssh-keygen is for the client ssh keys not the sshd service.
