NOTE: This was coordinated with human right activists, vulns reported, etc.
If you missed Hacking Mandated Apps - Part 1: Intro please start there for background 🙂
Translating APKs in beautiful exotic languages
As explained in the intro, the team did not get access to the sources of the app. We had to first retrieve the APK from a Korean APK download service, decompile the APK and then analyze the resulting sources.
With me being Spanish and Fabian being German, our Korean language skills were pretty much zero. So you can guess the challenge we faced when we first opened the app:
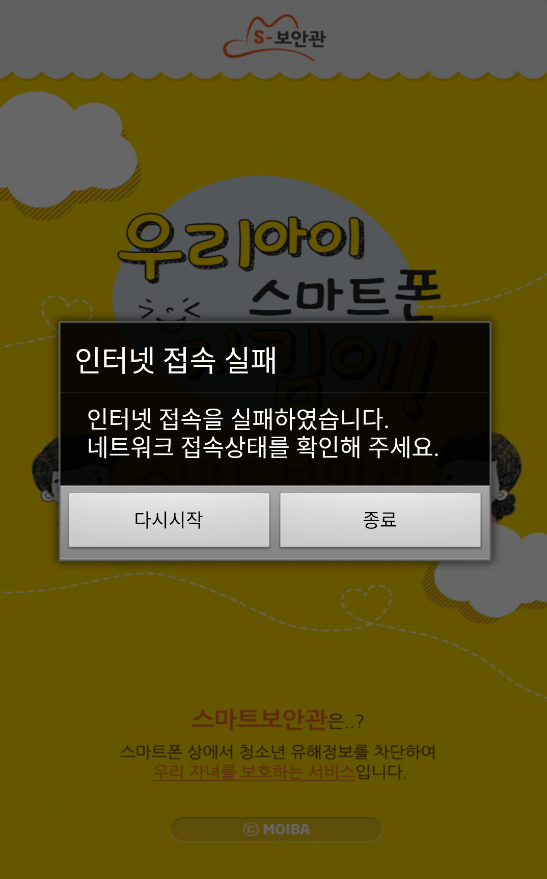 Fig.: Beautiful Korean characters in the original app
Fig.: Beautiful Korean characters in the original app
Thankfully, this is actually quite easy to solve:
1: Download and Install APKtool
2: Decompile the APK
apktool d smart_sheriff.apk -o smartsheriff_disassembled
3: Search for strings.xml
Command:
find . -name strings.xml
Output:
./smartsheriff_disassembled/res/values/strings.xml
4: Translate the XML file with Google Translate or a similar service (won't be perfect but gives you an idea!)
5: Replace strings.xml with the translated one
6: (Side note) If you don't have root, you probably also want to change the AndroidManifest.xml as follows (gives you file access via adb backup):
For more tips to test mobile apps without root, please see my presentation: Pwning Mobile Apps without Root or Jailbreak
7: Repackage the APK:
apktool b smartsheriff_disassembled -o smart_sheriff_english.apk
8: Sign the APK:
jarsigner -verbose -sigalg SHA1withRSA -digestalg SHA1 -keystore
my-release-key.keystore smart_sheriff_english.apk alias_name
9: Install the translated APK:
adb install smart_sheriff_english.apk
Hack Smart Sheriff to pieces with us!
NOTE: Attendants will get lifetime access to our training portal with:
- Unlimited course updates & Step-by-step lab video recordings
- Lots of real-world apps to practice with, such as:
+ Government-mandated and police apps in various countries
+ Many other excitingly vulnerable real-world apps!
+ IoT apps controlling Toys, Drones, etc.
- Global AppSec Amsterdam, EU: 23-25 September 2019
- c0c0n, Kochi, India: 25-26 September 2019
- LASCON, Austin, TX, USA: 22-23 October 2019
Cannot make it? ping sales@7asecurity.com for training portal access.
Recorded Talk 2: Area41
I believe the second time Fabian and myself presented this was at Area41:
Next blog post:
Hacking Mandated Apps - Part 3: What is SSL? [ MSTG-NETWORK-1 ]
