Are you testing MitM of an old protocol that starts using clear-text communications?
You should consider spoofing server replies with some downgrade attack!
This old trick still works sometimes against protocols that like:
XMPP, SMTP, POP3 and others
Let's illustrate this with an XMPP example from the field 🙂
Introduction:
In XMPP, credentials are not supposed to be sent in clear-text, instead, a challenge-response handshake is performed. For example, something like the following may be sent by the server:
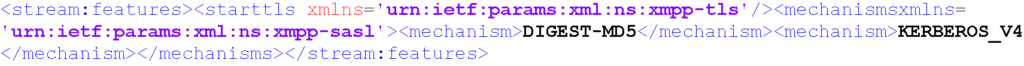
As you can see above, although clear-text is used during the handshake, only DIGEST-MD5 or KERBEROS_V4 are available to send credentials along, hence making the interception of credentials more difficult (vs. pure clear-text).
Please see the XMPP RFC 3920 for more information.
Attack: Clear-text XMPP MitM
Sometimes vulnerable clients may be attacked as follows:
Step 1: The attacker manipulates clear-text XMPP response
For example, during the initial clear-text XMPP handshake, we can say that the only available authentication mechanism is clear-text (PLAIN)
In English, this means the spoofed server reply says: Can you give me your creds please?

Unlike the previous example, in the above XMPP spoofed reply the attacker purposefully specifies the PLAIN mechanism as the only option to authenticate, hence leaving the client with no other option than revealing their credentials to the adversary.
Step 2: The mobile app sends credentials in plain text
In this case, the client was a mobile app vulnerable to this channel downgrade attack, and the clear-text credentials were sent along:

As you can see above, the base64-encoded string YWJlQDdhc2VjdXJpdHkuY29tAGY1ZGY0ZjY1LTZiM2MtNDk3OS1iM2RjLTA5MWExNjA0MGI1OA== is sent by the client, providing absolutely no security...
Step 3: The attacker base64-decodes the string
abe@7asecurity.com
f5df4f65-6b3c-4979-b3dc-091a16040b58
How to Fix clear-text XMPP MitM Vulnerabilities?
The first and ideal step would be to tunnel all XMPP traffic through TLS. The TLS protocol will then ensure communications are protected against integrity and confidentiality attacks.
If TLS is unavailable (seriously? in 2023?), the client should refuse to connect, ensuring no clear-text fallback is allowed.
If you liked this, you might also be interested in:
A FREE 4h Workshop: free-workshop-mobile-practical
Includes:
• 4h Video recording
• Vulnerable apps to practice
• Guided exercise PDF
• Lifetime access
More free stuff: 7asecurity free
Get 10% off any course: Course
Store: 7asecurity Store
Website: Click Here - 7asecurity.com
Upcoming training: training
Follow us:
Twitter: 7asecurity
LinkedIn: 7asecurity
YouTube: 7asecurity
Facebook: 7asecurity
